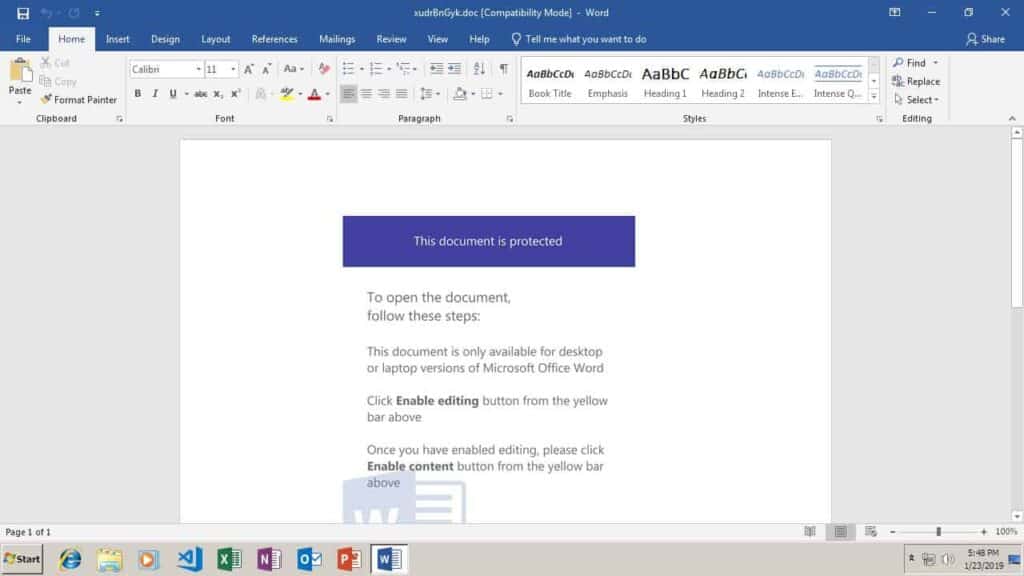
Emotet is a Trojan designed to steal banking information. It is frequently spread by sending phishing emails to governments, banks, healthcare organizations, and schools. The phishing emails will often claim to be an invoice, with a malicious Microsoft Word document attached. The email may often appear to be from a trusted supplier. Once the attachment or link is opened, the target is prompted to click “Enable content”, which would allow the dropper to install Emotet.
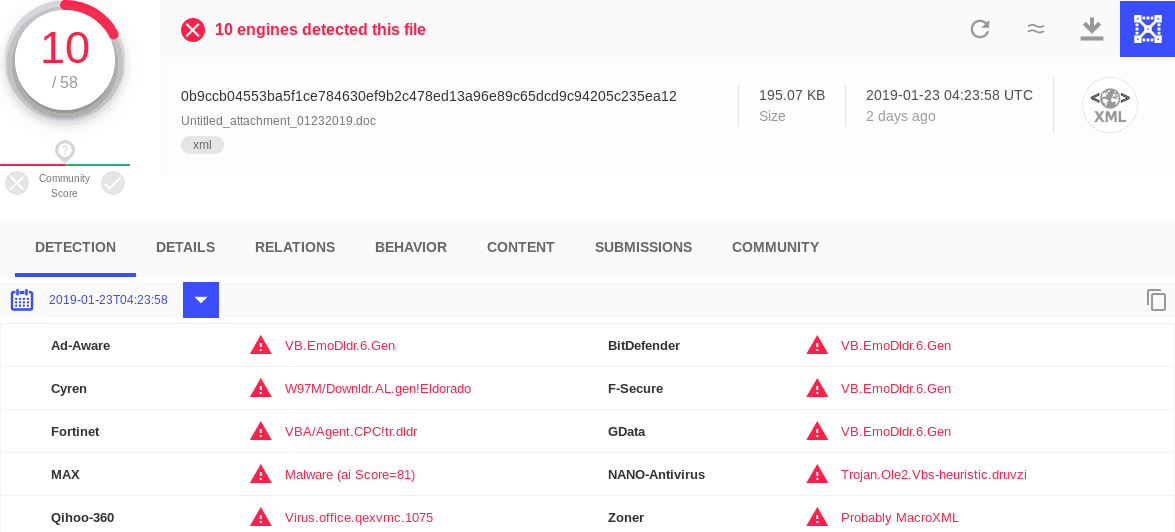
I recently encountered two Emotet dropper samples (0b9ccb04553ba5f1ce784630ef9b2c478ed13a96e89c65dcd9c94205c235ea12 and eff6619aee017ee5d04c539ff12c63a199a1e489660f7156b95e562667393d3c) that would not run correctly in my malware sandbox. I soon found the cause of the problem: the file type had been detected as a generic XML file, rather than what it really is: a Microsoft Word document.