
GoDaddy's email and Microsoft 365 customers are vulnerable to spoofing
Anyone with a GoDaddy server can create spoofed emails that pass SPF and DMARC, thanks to unauthenticated relays combined with lax documentation and an overly-broad SPF record

Anyone with a GoDaddy server can create spoofed emails that pass SPF and DMARC, thanks to unauthenticated relays combined with lax documentation and an overly-broad SPF record

Comprehensive notes for Google SecOps Analysts generated by Claude Opus 4.6
Chatting with Claude about the Pentagon banning Claude showed me exactly why it's so useful to the Intelligence Community
In a world where AI can do everything from writing code to creating graphics and planning strategies, employers will need far less humans

Multiple cases are still winding their way through the criminal justice system

A guide to using RECAP and PACER to analyze federal court cases like journalists do

A case study in how AI assistants like ChatGPT can help assert rights, as long as you check their output

You can host your own alterative to ChatGPT and access it on any device

With nginx, a domain name, and Let's Encrypt, all internal and external-facing web applications can use HTTPS — even on a home network
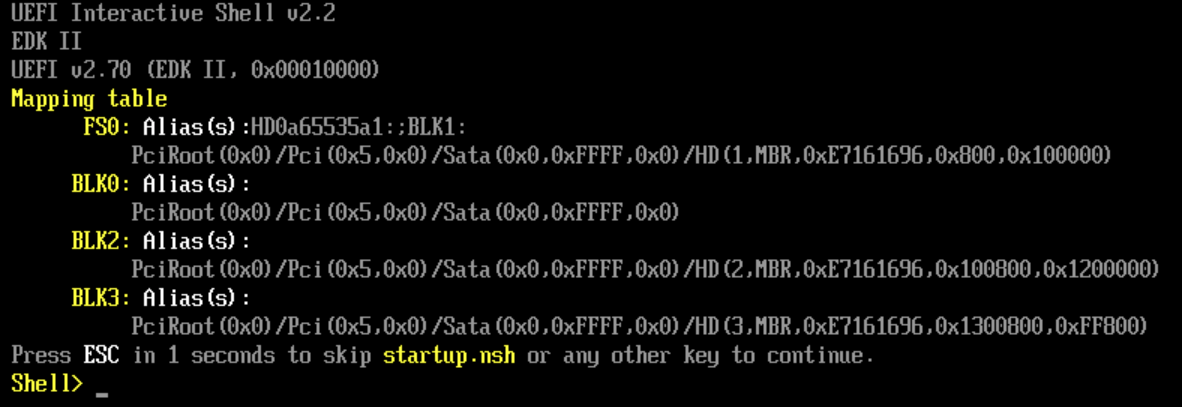
Navigation of the VM's BIOS menu and a Linux command will fix it