Business Email Compromise (BEC) attacks are easy, cheap, and often very effective. This high Return on Investment makes BEC an extremely popular with attackers of any skill level—from low-level scammers to state-sponsored groups. BEC occurs when an attacker is able to access an email inbox within a business. From there, an attacker examine sensitive emails, insert themselves into email threads, and spread phishing emails from the trusted email account. While BEC can be devastating to the finances, reputation, and operations of any business, small businesses are particularly vulnerable. Fortunately. the defenses against BEC such as multi-factor authentication and user training are also simple, cheap and effective.
phishing
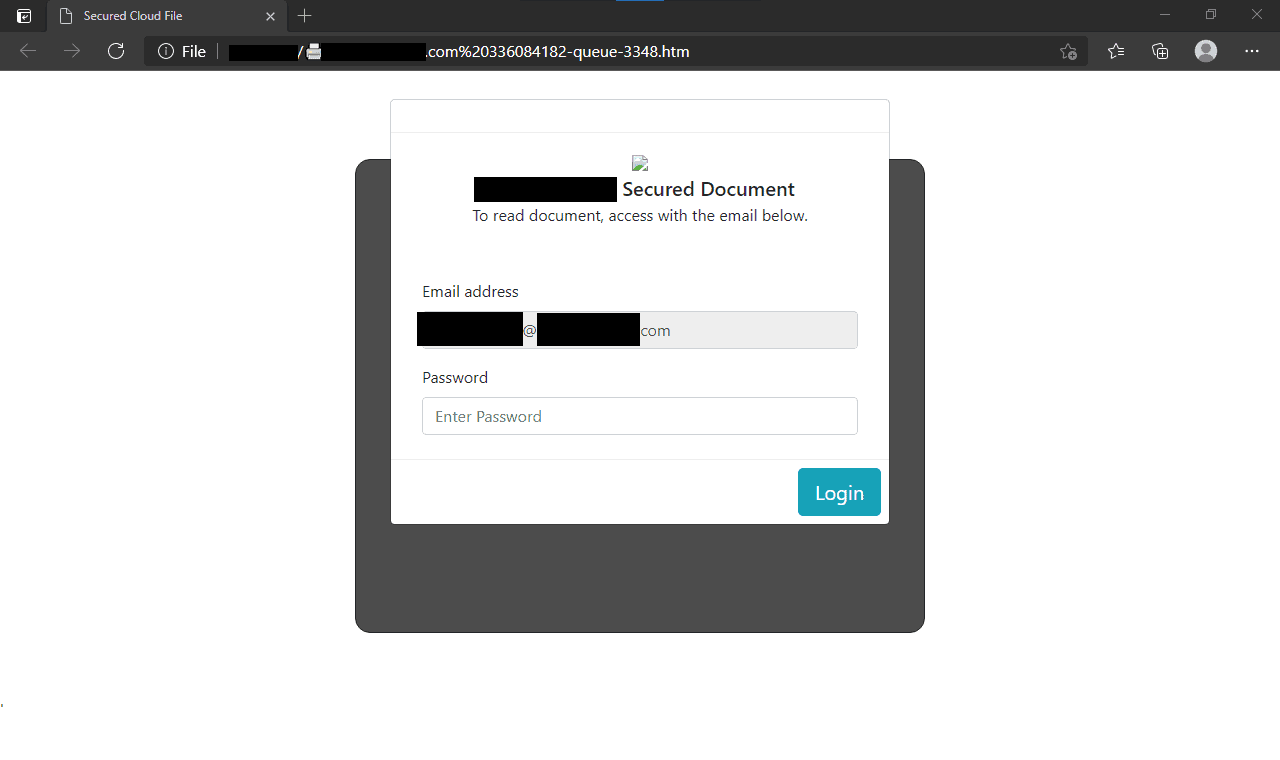
How to examine a credential harvesting page using Microsoft Edge
Recently I analyzed a credential harvesting page with some interesting characteristics that made a great teaching moment. In this post, I’ll go over how I used the developer tools built into Microsoft Edge to examine the credential harvesting page.