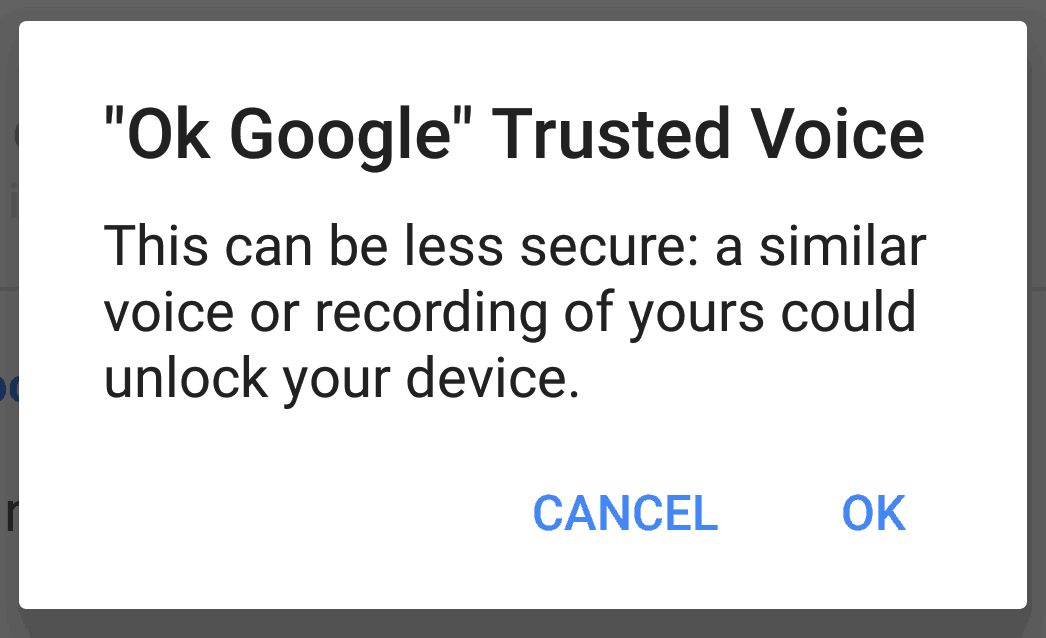
The headline feature of the new Google Pixel phones is deep integration between the operating system and the Google Assistant AI. By default, the Google Assistant can be activated even when the phone is locked and the display is off, if the device hears the trusted voice say the hot word, “Ok Google”. This also has the effect of unlocking the device, meaning that anyone with a recording of the trusted voice saying “Ok Google” — or even someone with a similar voice — can easily unlock the device.
privacy
HHS: Ransomware encryption of ePHI is a HIPAA breach
As a growing number of medical facilities are struck by ransomware, the US Department of Health and Human Services (HHS) has published a fact sheet describing how businesses that process electronic Protected Health Information (ePHI) should defend against and respond to ransomware.
DoJ v. Apple: It’s all about the precedent
By now, you’ve probably heard something about the ongoing legal battle between Apple and the Department of Justice. “DoJ v. Apple” coverage has been abundant, on blogs and TV news shows alike, but in case you haven’t here’s a quick recap. The FBI obtained the work iPhone of Syed Rizwan Farook, who, along with his wife Tashfeen Malik, murdered 14 people in a shooting rampage at a holiday party in San Bernardino, California. The government suspects that iPhone may hold critical information about the couple’s contacts in the weeks leading up to the attacks – contacts that may uncover future plots. They have a warrant, but they can’t access the data on the phone because it is using the strong encryption that comes with iOS 9 and up. Not even Apple can bypass the encryption, at least directly.